










CT10 is an advanced access control terminal featuring a camera and four authentication methods, including mobile credentials (BLE/NFC), RFID cards, QR scanning, and keypad input. It supports flexible connectivity via Ethernet, 4G, WiFi, and LoRaWAN for real-time or standalone operation. With an open SDK and customizable 3.5-inch touch interface, it enables tailored integration across corporate, industrial, and smart building applications.
| CT10 IDENTIFICATION | |
|---|---|
| RFID | 125KHz PROX™, EM; 13.56MHz Mifare® Classic, Ultralight®, Plus, DESFire® EV1/EV2/EV3, NFC tags |
| Mobile Credential | BLE, NFC, QR Code |
| Keypad | Supported (Touch Screen) |
| GENERAL & INTERFACE | |
| Operating System | LINUX OS |
| Display | 3.5" touch screen (Resistant to UV ray) |
| Camera | Autofocus with LED Flash |
| Communication | TCP/IP (RJ45), WiFi, LoRaWAN, 4G, RS485, Wiegand |
| I/O Ports | Door contact, Exit button, Buzzer control, Tamper alarm |
| CAPACITY & INSTALLATION | |
| Max Users | 100,000 (Local); Unlimited (Online) |
| Event Logs | 200,000 logs; 7,000 Image logs |
| Power Supply | DC 12~24V or PoE IEEE802.3af |
| Dimensions | 198mm(H) * 82.6mm(W) * 46mm(D) |
| Protection | IP65 Rated, UV Resistant, Operation Temp: -20~60ºC |

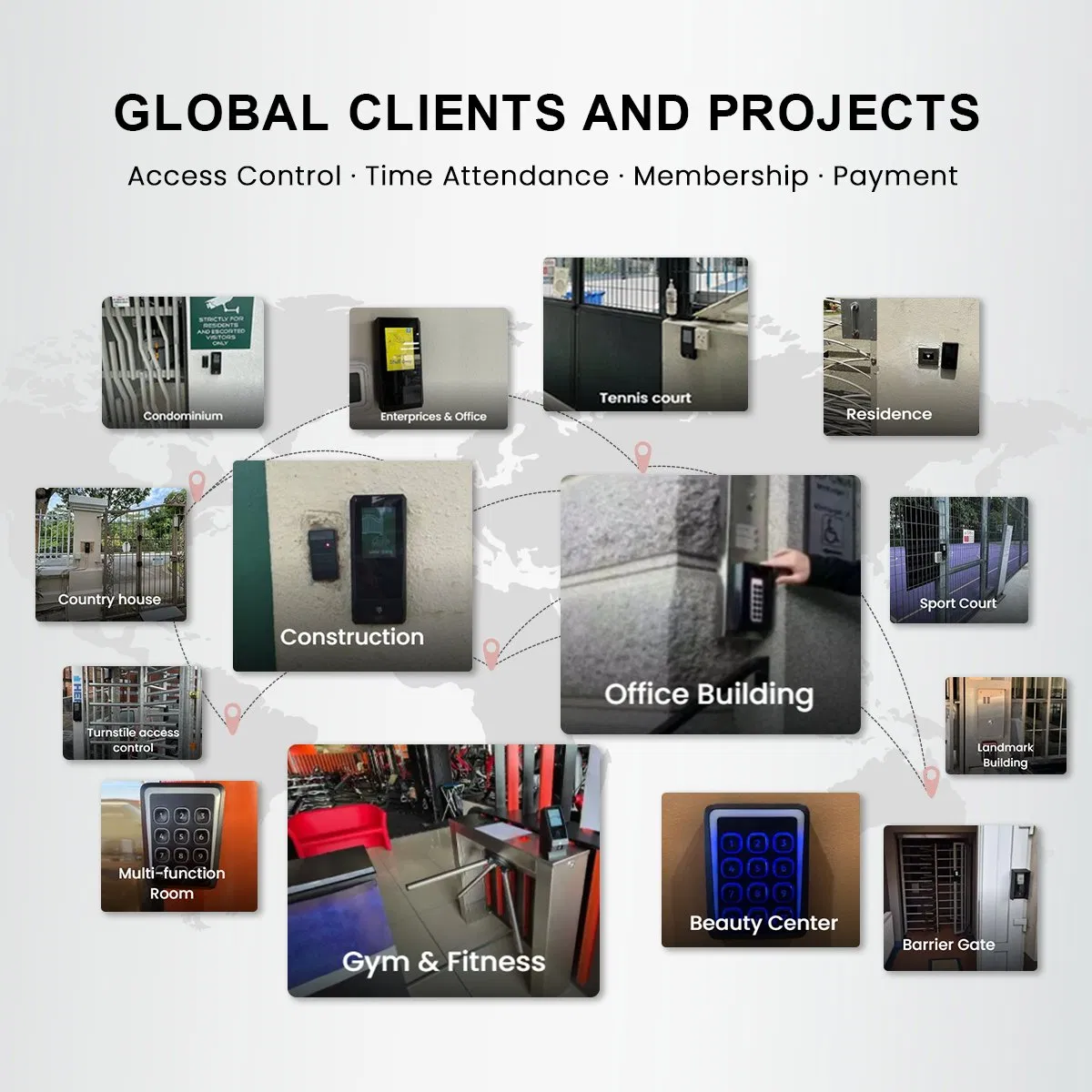
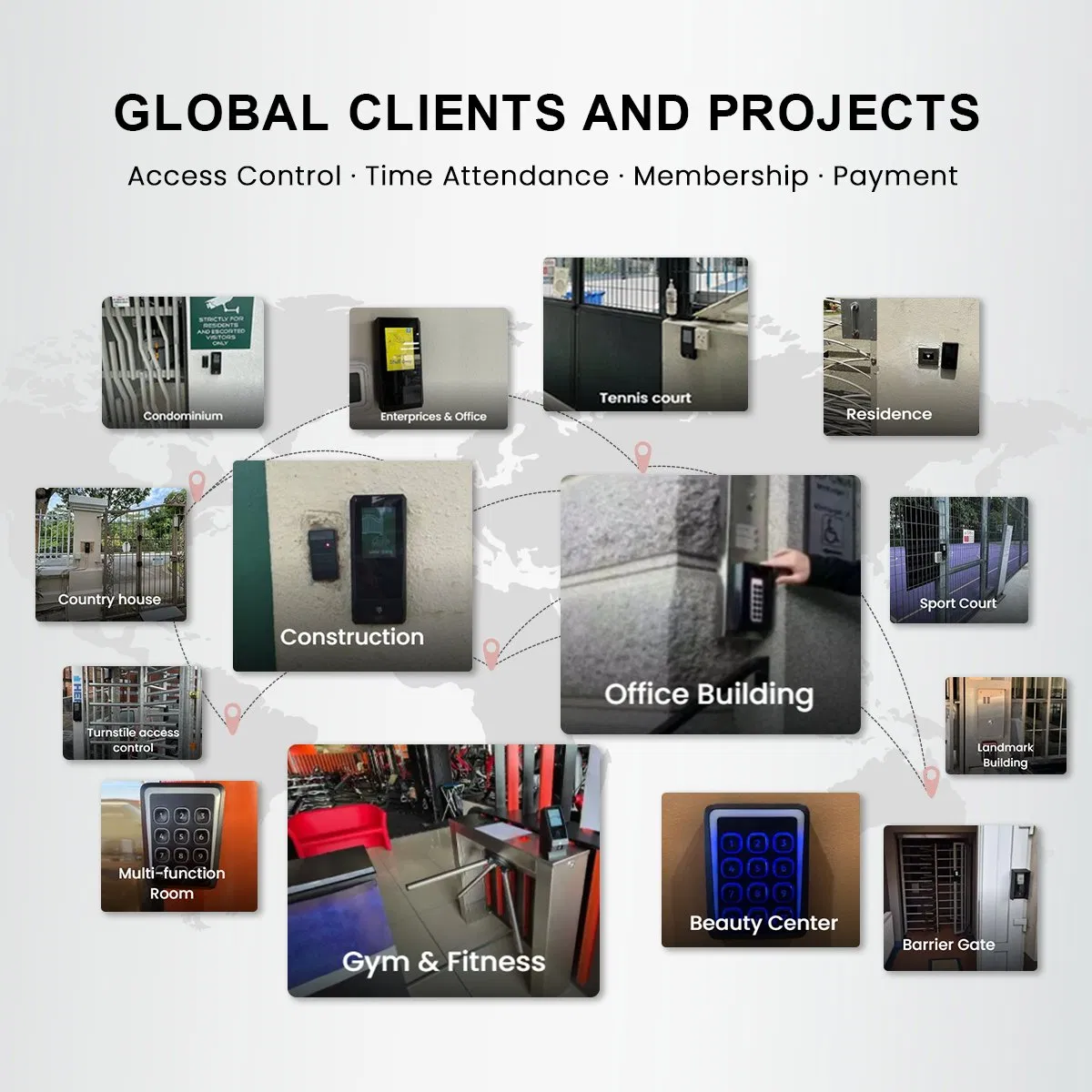
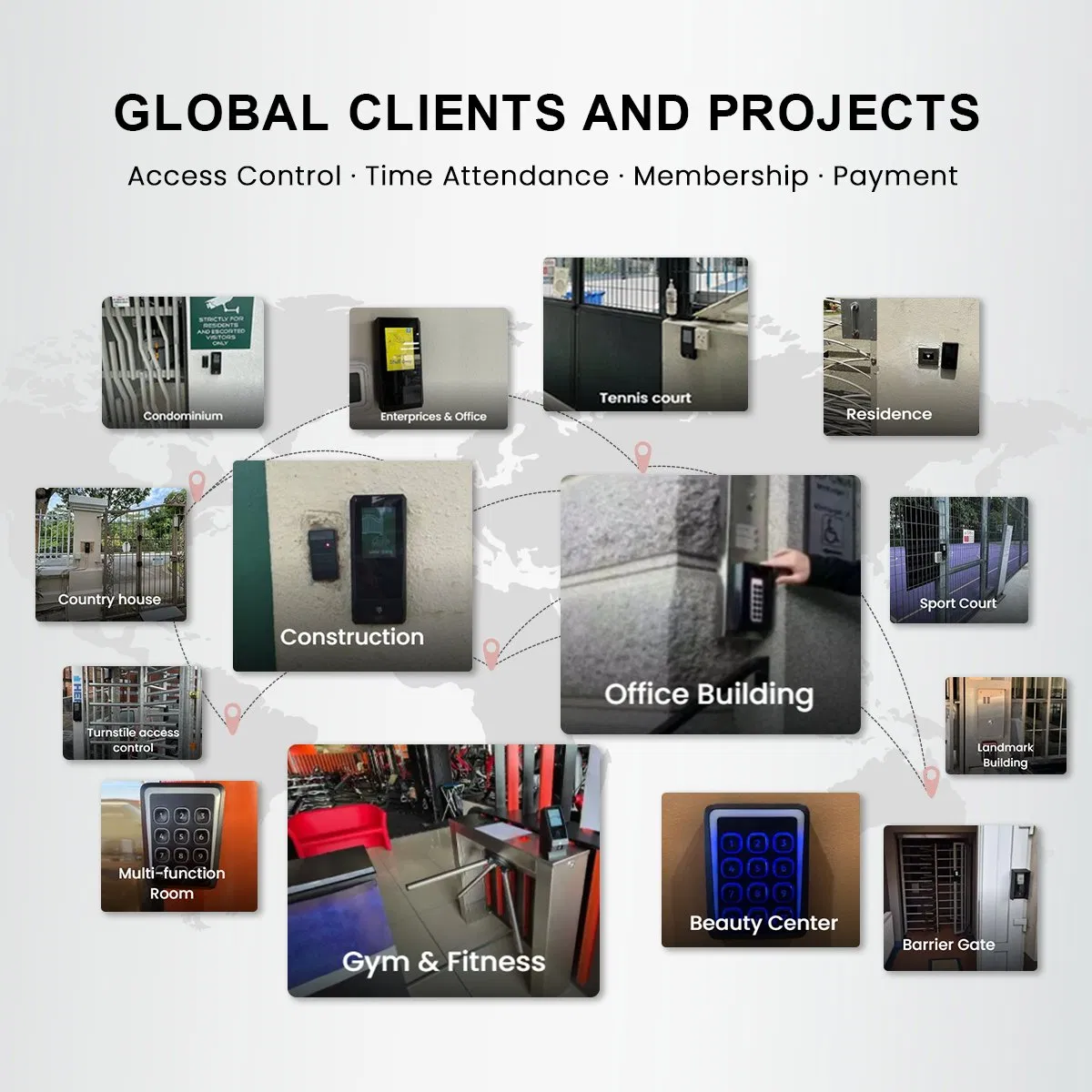
Support Multiple Authentication Technologies
Combine mobile App, digital credentials, and physical cards for enhanced security.

Cloud Management: Real-time remote control of locks and facilities via encrypted HTTP/HTTPS.

4G + GPS: Reliable outdoor connectivity and location verification for remote construction sites.

AES Encryption: Advanced protection for digital credentials and communication protocols.

Weather-Resistant: Compact mullion design with robust IP65 housing for any environment.

Auto Image Record: Automatically captures snapshots upon access for a clear visual audit trail.
A robust SDK with demo software is provided for third-party server integration. The hardware testing package includes all necessary accessories and software tools for easy configuration, fast development, and seamless firmware upgrades.

We offer comprehensive customization services including hardware modifications, reader housing design, firmware adjustments, and specialized software development to meet unique project requirements.